Drive
Invest
Data Corruption
Data Lifespan
Deep Fakes
|
|
Home | Eon
Drive |
Diom Block | Contact
Invest |
||
| No more ➜ | Blockchain Data Corruption Data Lifespan |
Fear of Looming Quantum Computers | Fake News Deep Fakes |
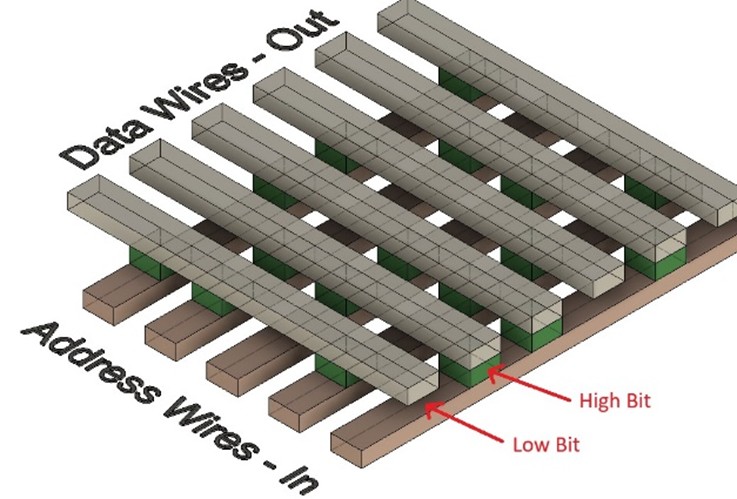
DiomBlockWhile Diom Eon Drive is a device for storing large volumes of permanent memory, Diom Block prepares one-off or low-run read-only memory for integration directly into electronic products. Diom Block products typically store either cryptographic keys, hashing nonces, or secure machine instructions, providing the following product types:
Diom Key and Diom Truth – Secure Communication and AuthenticationA mature product version of 3D-Printed ROM would allow the low-cost printing of crypto key pairs at a space density of approximately 100 GBytes per cm³, and a weight of 2–5 grams per cm³. This enables deployment of sufficient crypto key pairs for the lifetime of a mobile product, removing the necessity for reliance on asymmetric public-key methods. By hardware-controlled, single-use drip-feeding of stored keys, and assuming a maximum 10-year product life with 10 hours of use per day (36,500 hours total), 1 cm³ of memory would provide approximately 2.74 MB of symmetric private key data per hour for one-time-pad encryption — or about 87,000 individual 256-bit key pairs for use with algorithm families such as AES and SHA. This is more than sufficient for many applications, including:
Currently, mimicking a mobile device over a network — while difficult — is technically feasible and practically achievable with moderate but not extraordinary resources. Diom Key and Diom Truth aim to make such attacks infeasible at the hardware level. Diom Code – Secure CodeComputers are essentially machines that follow a list of predefined instructions, or code. When that code is stored on a mutable medium, the machine can be reprogrammed to do anything within its capabilities without changing any physical component. Computers now control an ever-increasing number of systems — from washing machines and household lighting to the brakes in your car and even defense drones. Ideally, code controlling critical applications or systems should not change. However, it is often stored on mutable, rewritable memory. The common rationale is that replacing ROM when code changes are needed after deployment is costly. While true to an extent, this approach introduces a significant security vulnerability, because:
Software updating facilities are now standard, even in basic systems, and these operate across the public Internet using indecipherable machine code that may contain malicious payloads without detection. Malicious code that self-erases after execution could be deployed, and no one would ever know. This approach is a major security flaw and, when combined with duplication and hybrid methods described earlier, is likely responsible for many of the cybersecurity issues reported today. 3D-Printed ROM provides a low-cost method of preparing control code for critical and secure operations — including computer startup and OS-level code — ensuring that no one can alter critical functionality by modifying the underlying system software. The secure code can be packaged with a low-cost disposable CPU in a tamper-resistant form, requiring physical replacement to update. This creates a hardened hardware/software boundary for critical systems. Diom ID and Diom LockCurrently, PCs and many devices possess unique identifiers that can be mimicked by other systems. This means there is no reliable way to verify a device’s true identity across a network. Software-based identifiers can be cloned, leaving manufacturers, organizations, and even governments uncertain about which machine they are communicating with. Similarly, while numerous cryptographic and hashing methods exist, nothing prevents malicious duplication of a PC’s operating system and interface to simulate encryption or content verification — deceiving the user into thinking communication is secure when it is not. Door locks and RFID systems generally rely on small memories and weak encryption keys. These are frequently compromised. Many existing systems are designed around convenience and centralised control, not true physical security. Diom ID uses a fresh portion of a very long key for each authentication cycle (or within a short time slice). With tamper-detection and self-destructive memory features, cloning becomes exceedingly difficult. This allows remote verification of untampered devices across networks. Diom Lock extends this approach to access control. It enables the secure exchange of partial key data between nodes such as a lock and a wireless key, based on a hierarchical permission system. This allows homeowners and small businesses to implement contactless, distributed, offline locking systems that do not depend on centralized networks or Internet connectivity. |
Application Areas:1. Financial Transaction Records 2. Identity and Government Records 3. Legal Records & Contracts 4. Revision Documentation Management (Engineering Drawings, BIM models) 5. Communication Records (e-mails, and legal correspondence) 6. Secure Code (Code for critical or secure applications) 7. Device or Content Source ID 8. Digital Content Authentication (Prevents deep fakes) 9. Product tracing, and authentication |